linux openssl是什么
在linux中,openssl是一个功能极其强大的命令行工具,可以用来完成公钥体系及HTTPS相关的很多任务。openssl有两种运行模式:交互模式和批处理模式;直接输入openssl回车进入交互模式,输入带命令选项的openssl进入批处理模式。
本教程操作环境:linux7.3系统、Dell G3电脑。
一、openssl命令简介
openssl是一个功能极其强大的命令行工具,可以用来完成公钥体系(Public Key Infrastructure)及HTTPS相关的很多任务。openssl是一个强大的安全套接字层密码库,囊括主要的密码算法、常用的密钥和证书封装管理功能及SSL协议,并提供丰富的应用程序供测试或其它目的使用。
openssl有两种运行模式:交互模式和批处理模式。直接输入openssl回车进入交互模式,输入带命令选项的openssl进入批处理模式。
openssl整个软件包大概可以分成三个主要的功能部分:密码算法库、SSL协议库以及应用程序。openssl的目录结构自然也是围绕这三个功能部分进行规划的。 openssl命令的作用:
- 私钥、公钥和参数的创建和管理
- 公开密钥加密操作
- 创建X.509证书、CSR和CRL
- 信息摘要的计算
- 使用密码进行加密和解密
- SSL/TLS客户端和服务器测试
- 处理S/MIME签名或加密邮件
- 时间戳请求、生成和验证
二、使用示例
1、交互模式下获取命令帮助
OpenSSL> help Standard commands asn1parse ca ciphers cms crl crl2pkcs7 dgst dhparam dsa dsaparam ec ecparam enc engine errstr gendsa genpkey genrsa help list nseq ocsp passwd pkcs12 pkcs7 pkcs8 pkey pkeyparam pkeyutl prime rand rehash req rsa rsautl s_client s_server s_time sess_id smime speed spkac srp storeutl ts verify version x509 Message Digest commands (see the `dgst’ command for more details) blake2b512 blake2s256 gost md4 md5 mdc2 rmd160 sha1 sha224 sha256 sha3-224 sha3-256 sha3-384 sha3-512 sha384 sha512 sha512-224 sha512-256 shake128 shake256 sm3 Cipher commands (see the `enc’ command for more details) aes-128-cbc aes-128-ecb aes-192-cbc aes-192-ecb aes-256-cbc aes-256-ecb aria-128-cbc aria-128-cfb aria-128-cfb1 aria-128-cfb8 aria-128-ctr aria-128-ecb aria-128-ofb aria-192-cbc aria-192-cfb aria-192-cfb1 aria-192-cfb8 aria-192-ctr aria-192-ecb aria-192-ofb aria-256-cbc aria-256-cfb aria-256-cfb1 aria-256-cfb8 aria-256-ctr aria-256-ecb aria-256-ofb base64 bf bf-cbc bf-cfb bf-ecb bf-ofb camellia-128-cbc camellia-128-ecb camellia-192-cbc camellia-192-ecb camellia-256-cbc camellia-256-ecb cast cast-cbc cast5-cbc cast5-cfb cast5-ecb cast5-ofb des des-cbc des-cfb des-ecb des-ede des-ede-cbc des-ede-cfb des-ede-ofb des-ede3 des-ede3-cbc des-ede3-cfb des-ede3-ofb des-ofb des3 desx idea idea-cbc idea-cfb idea-ecb idea-ofb rc2 rc2-40-cbc rc2-64-cbc rc2-cbc rc2-cfb rc2-ecb rc2-ofb rc4 rc4-40 seed seed-cbc seed-cfb seed-ecb seed-ofb sm4-cbc sm4-cfb sm4-ctr sm4-ecb sm4-ofb登录后复制
2、查看命令版本
OpenSSL> version OpenSSL 1.1.1h 22 Sep 2020登录后复制
3、利用openssl命令进行base64编码和解码
- base64编码
(base) [root@sun-site certs]# echo “wuhs” |openssl base64 d3Vocwo= (base) [root@sun-site certs]# echo “wuhs” > 1.txt (base) [root@sun-site certs]# openssl base64 -in 1.txt d3Vocwo=登录后复制
- base64解码
(base) [root@sun-site certs]# echo “d3Vocwo=” | openssl base64 -d wuhs (base) [root@sun-site certs]# openssl base64 -d -in 1.base64 wuhs登录后复制
4、利用openssl生成随机密码
- 生成12位的随机密码
(base) [root@sun-site certs]# openssl rand -base64 10 |cut -c 1-12 PGznlV5Og0Us登录后复制
5、利用openssl命令生成摘要
- 对字符串“wuhs”进行md5摘要计算
(base) [root@sun-site certs]# echo wuhs | openssl md5 (stdin)= 4cdb1fbd6a34ff27dc8c10913fab3e7e (base) [root@sun-site certs]# openssl md5 1.txt MD5(1.txt)= 4cdb1fbd6a34ff27dc8c10913fab3e7e登录后复制
- 对字符串“wuhs”进行sha1摘要计算
(base) [root@sun-site certs]# openssl sha1 1.txt SHA1(1.txt)= bd8f0b20de17d623608218d05e8741502cf42302 (base) [root@sun-site certs]# echo wuhs | openssl sha1 (stdin)= bd8f0b20de17d623608218d05e8741502cf42302登录后复制
6、利用openssl命令进行AES加密解密
- 对字符串“wuhs”进行aes加密,使用密钥123,输出结果以base64编码格式给出
(base) [root@sun-site certs]# openssl aes-128-cbc -in 1.txt -k 123 -base64 *** WARNING : deprecated key derivation used. Using -iter or -pbkdf2 would be better. U2FsdGVkX194Z8P5c7C8vmXbA39omlqU/ET8xaehVFk=登录后复制
- 将aes加密文件数据进行解密,密钥123
(base) [root@sun-site certs]# openssl aes-128-cbc -d -k 123 -base64 -in 2.txt *** WARNING : deprecated key derivation used. Using -iter or -pbkdf2 would be better. wuhs登录后复制
7、密钥生成与验证
- 创建加密的私钥
(base) [root@sun-site tmp]# openssl genrsa -des3 -out sunsite.key 2048 Generating RSA private key, 2048 bit long modulus (2 primes) …+++++ …+++++ e is 65537 (0x010001) Enter pass phrase for sunsite.key: Verifying - Enter pass phrase for sunsite.key: (base) [root@sun-site tmp]# ll total 16 -rw------- 1 root root 1751 Oct 25 14:43 sunsite.key登录后复制
- 验证私钥
(base) [root@sun-site tmp]# openssl rsa -check -in sunsite.key Enter pass phrase for sunsite.key: RSA key ok writing RSA key -----BEGIN RSA PRIVATE KEY----- MIIEpAIBAAKCAQEA1jDreCAjX5kpNmnyNayQB/GUvyIRvZZM2WoKAIjne91JupgP OKmBdYSWeWsf0h0XU9ubhCHpgCss2hdRKxLN3rJLlFD98TUKpb9S2XkfrT9s3cLN PQyCELK60zrs1sE52I4pDj4nTZPZCL9mykzqwNa5rcGuHN/lLnvJxFPJOJwVWbVE Bvh+jGioJbi+Ar0rs37/8naGBYz5k4BFn5sCKrhssoMEpDWjMz4yJMpycTlEFITa …登录后复制
- 加密私钥,输入密码后私钥文件完成加密
(base) [root@sun-site tmp]# openssl rsa -des3 -in sunsite.key -out sunsite.key writing RSA key Enter PEM pass phrase: Verifying - Enter PEM pass phrase:登录后复制
- 解密私钥,输入密码后私钥文件被解密
(base) [root@sun-site tmp]# openssl rsa -in sunsite.key -out sunsite2.key Enter pass phrase for sunsite.key: writing RSA key登录后复制
8、生成证书签名
- 使用指定私钥文件生产csr文件
(base) [root@sun-site tmp]# openssl req \ -key sunsite.key \ -new -out sunsite.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:CN State or Province Name (full name) [Some-State]:HuNan Locality Name (eg, city) []:changsha Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com Please enter the following ‘extra’ attributes to be sent with your certificate request A challenge password []:123456 An optional company name []:123456登录后复制
- 生成私钥和CSR
(base) [root@sun-site tmp]# openssl req \ -newkey rsa:2048 -nodes -keyout s.key \ -out s.csr Generating a RSA private key …+++++ .+++++ writing new private key to ‘s.key’ ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hunan Locality Name (eg, city) []:changsha Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com Please enter the following ‘extra’ attributes to be sent with your certificate request A challenge password []:123456 An optional company name []:123456 (base) [root@sun-site tmp]# ll total 28 -rw-r–r-- 1 root root 1102 Oct 25 15:37 s.csr -rw------- 1 root root 1708 Oct 25 15:37 s.key登录后复制
- 使用已有的证书和私钥生成CSR
openssl x509 \ -in domain.crt \ -signkey domain.key -x509toreq -out domain.csr登录后复制
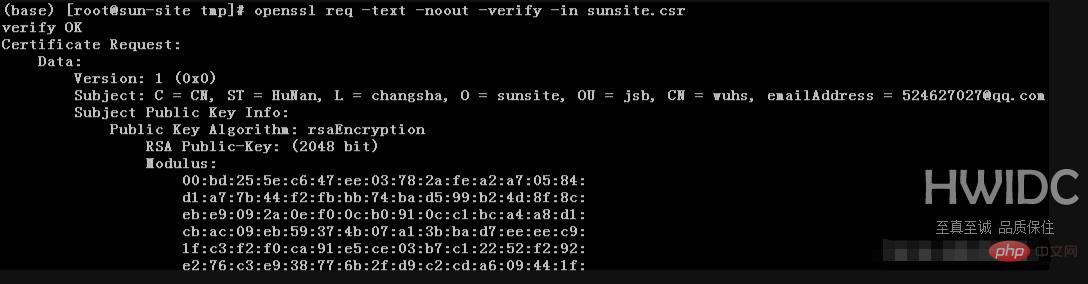
- 查看CSR文件
(base) [root@sun-site tmp]# openssl req -text -noout -verify -in sunsite.csr登录后复制
9、制作和查看SSL证书
- 生成自签名证书
(base) [root@sun-site tmp]# openssl req \ -newkey rsa:2048 -nodes -keyout sunsite.key \ -x509 -days 365 -out sunsite.crt Generating a RSA private key …+++++ …+++++ writing new private key to ‘sunsite.key’ ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hn Locality Name (eg, city) []:cs Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com (base) [root@sun-site tmp]# ll -rw-r–r-- 1 root root 1383 Oct 25 16:03 sunsite.crt -rw-r–r-- 1 root root 1102 Oct 25 15:05 sunsite.csr -rw------- 1 root root 1708 Oct 25 16:03 sunsite.key登录后复制
- 使用已有私钥生成自签名证书
(base) [root@sun-site tmp]# openssl req \ -key sunsite.key -new \ -x509 -days 365 -out sunsite.crt You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hn Locality Name (eg, city) []:cs Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:wuhs@qq.com登录后复制
- 使用已有的私钥和CSR生成自签名证书
(base) [root@sun-site tmp]# openssl x509 \ -signkey sunsite.key \ -in sunsite.csr \ -req -days 365 -out sunsite.crt Signature ok subject=C = CN, ST = HuNan, L = changsha, O = sunsite, OU = jsb, CN = wuhs, emailAddress = 524627027@qq.com Getting Private key登录后复制
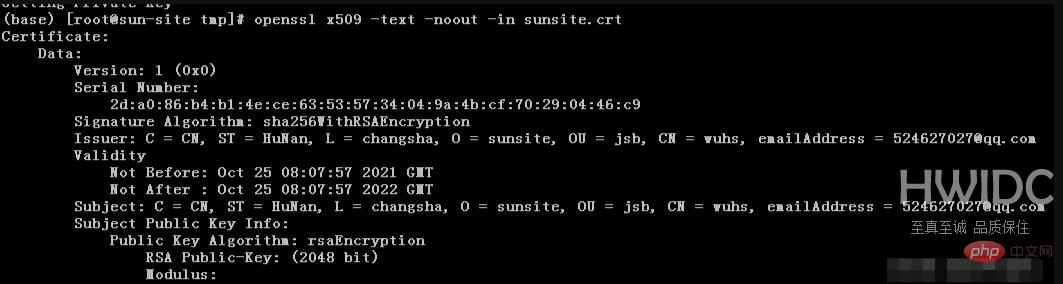
- 查看证书
(base) [root@sun-site tmp]# openssl x509 -text -noout -in sunsite.crt
- 验证证书是否由ca颁发
(base) [root@sun-site tmp]# openssl verify -verbose -CAfile ca.crt sunsite.crt Error loading file ca.crt #需要ca证书登录后复制
- 验证私钥、证书、CSR是否匹配
(base) [root@sun-site tmp]# openssl x509 -noout -modulus -in sunsite.crt |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 (base) [root@sun-site tmp]# openssl rsa -noout -modulus -in sunsite.key |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 (base) [root@sun-site tmp]# openssl req -noout -modulus -in sunsite.csr |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 #md5校验和一致说明,三者匹配登录后复制
10、证书格式转换
- PEM转DER
(base) [root@sun-site tmp]# openssl x509 -in sunsite.crt -outform der -out sunsite.der登录后复制
- DER转PEM
(base) [root@sun-site tmp]# openssl x509 -in sunsite.der -inform der -out sunsite.crt登录后复制
- PEM转PKCS7
(base) [root@sun-site tmp]# openssl crl2pkcs7 -nocrl -certfile sunsite.crt -certfile ca-chain.crt -out sunsite.p7b登录后复制
- PKCS7转换为PEM
#openssl pkcs7 -in domain.p7b -print_certs -out domain.crt登录后复制
- PEM转换为PKCS12
openssl pkcs12 -inkey domain.key -in domain.crt -export -out domain.pfx登录后复制
- PKCS12转换为PEM
openssl pkcs12 -in domain.pfx -nodes -out domain.combined.crt登录后复制
11、证书吊销
- 客户端获取要吊销证书的serial(在使用证书的主机执行)
(base) [root@sun-site tmp]# openssl x509 -in sunsite.crt -noout -serial -subject serial=2DA086B4B14ECE63535734049A4BCF70290446C9 subject=C = CN, ST = HuNan, L = changsha, O = sunsite, OU = jsb, CN = wuhs, emailAddress = 524627027@qq.com登录后复制
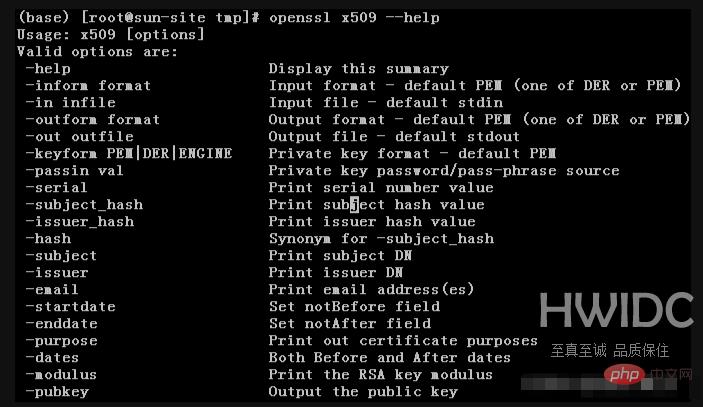
12、获取命令帮助
- 以openssl x509命令为例
(base) [root@sun-site tmp]# openssl x509 --help
三、使用语法及命令介绍
1、使用语法
openssl command [ command_opts ] [ command_args ]登录后复制
2、标准命令
s_timeSSL连接计时器。sess_idSSL会话数据管理。smimeS/MIME邮件处理。speed算法速度测量。spkacspkac打印和生成实用程序ts时间戳授权工具(客户端/服务器)verifyX.509证书验证。versionOpenSSL版本信息。x509X.509证书数据管理。
3、消息摘要命令
4、编码和密码命令
相关推荐:《Linux视频教程》
以上就是linux openssl是什么的详细内容,更多请关注海外IDC网其它相关文章!
【转自:美国高防服务器 http://www.558idc.com/usa.html转载请说明出处】